Year in review 2021: Top 5 things that happened in cyber security
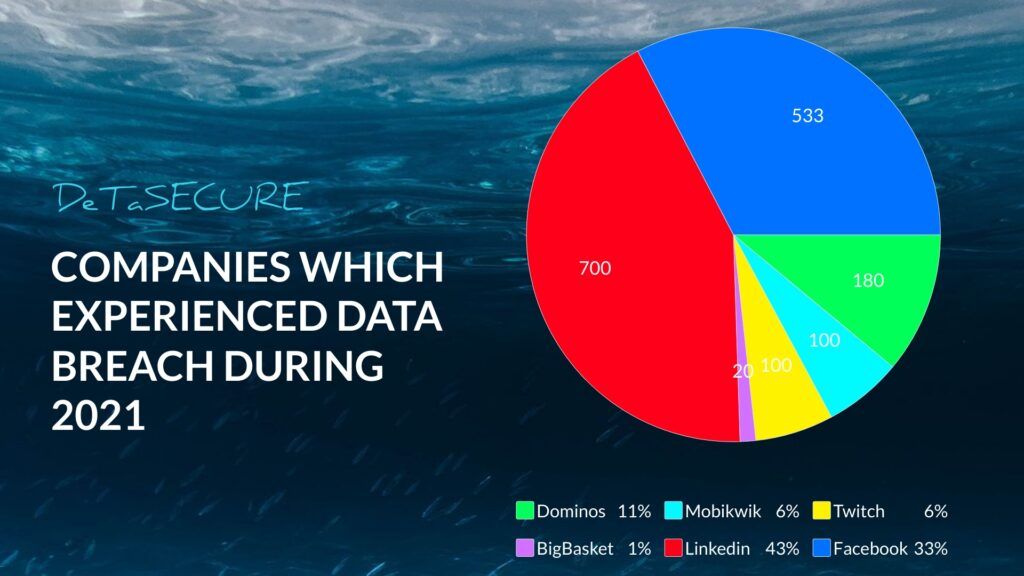
Hello Hackers. Hope you are all doing good; 2021 is likely to be the year of a data breach because many big tech companies like Facebook, Linkedin, Big basket, twitch, and others were also affected. But we are not going to discuss all of them in this blog post, ok without wasting much time, let us take a quick recap on what are all the things that happened during this year.
Let’s get started
#1 Mobikwik data breach:

Earlier this year, Mobikwik suffered a massive data breach that exposed 6 TB of user data containing Email addresses, phone numbers, PAN cards, Adhaar cards, and other personal information. However, This, on the other hand, is the largest data breach in history. But Mobikwik denied this leak and said that “It is entirely possible that any user could have uploaded her/ his information on multiple platforms. Hence, it is incorrect to suggest that the data available on the dark web has been accessed from MobiKwik or any identified source.”
#2 Dominos data breach:

Like Facebook, Linkedin, and Mobikwik, Dominos also experienced a data breach. Mainly Indians are the primary target of this data breach. The leaked data including Email addresses, phone numbers, credit card details, the amount spent, the total number of orders, location of the order, and other sensitive information are also disclosed. Hackers have created a search engine in the dark web to query this information and were selling the data in exchange for cryptocurrency.
#3 Colonial pipeline attack:
The Colonial pipeline is the largest fuel-carrying pipeline system in the United States, and it was hacked by the hacker's group named Darkside. This attack leads to shutting down the entire pipeline system for the first time in its 57-year history. However, the colonial company paid the ransom of 75 bitcoin which was worth $4.4 million to recover its data. But, with the help of the FBI and Fireye, the colonial can able to get the ransom back.
#4 Pegasus:
Pegasus is an android malware created by NSO Group. The purpose of this malware is for government organizations to spy on terrorists. But the leaked database has 50,000 phone numbers that were aimed at journalists, political leaders, and Ministers. pegasus can be installed remotely on a smartphone without requiring any action from its owner and allows the malware operators to take complete control of the device, including accessing messages from encrypted messaging apps like WhatsApp and Signal, and enabling the microphone and camera and even tracking real-time location.
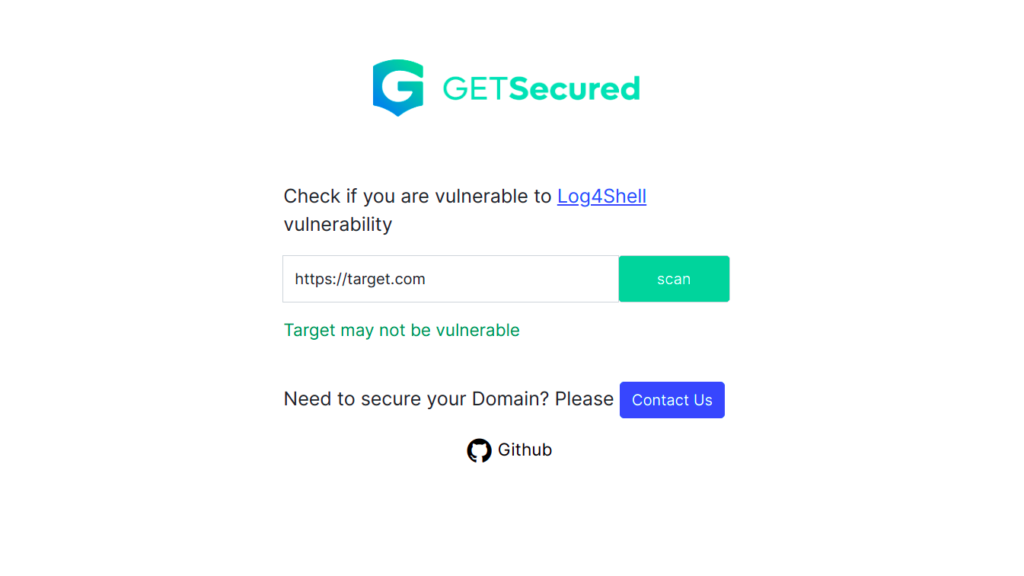
#5 Log4j vulnerability:

Log4j is a java-based logging framework. The vulnerability in this framework allows an attacker to execute the code remotely. However, This vulnerability affects the majority of the internet. Security researchers from all over the world started looking out for this flaw. Many companies are willing to pay up to $25,000 only for this bug. Even a person with very little technical knowledge can also exploit this vulnerability. If you want to know more about log4j vulnerability, check out this nice article here. You can also check if you are vulnerable or not in this amazing tool, that DeTaSECURE provides as a “FREE” service.
https://log4shell.getsecured.ai/
Final thoughts:
Nowadays cybercriminals are evolved and cybercrime is also growing exponentially, So If you want to secure your organization from cyber threats we DeTaSECURE is there for you!!! DeTaSECURE provides a tool called getsecured.ai. It will find source code leakage, breached data, all vulnerabilities present in your web application, and many more.
Yuvarajan
is working as a security engineer in Detasecure. He can able to perform memory forensics and can able to analyze malware. He has done B.E from Anna University. He is an active participant in capture the flag (CTF) competitions. You can reach out to him by Clicking Here.
